Google is already fighting hackers from the future with post-quantum cryptography
BY STAN SCHROEDER for Mashable
For years, experts have warned users to use secure browser communications whenever possible. If you visit a site and the URL in your browser’s address bar starts with “https://”, you know the communication between your computer and the server is encrypted.
But that encryption, according to Google, has a potential weakness. If quantum computers get sufficiently powerful in the future, they could be used to break TLS, the cryptographic protocol that’s one of the foundations of HTTPS.
Worse, a future quantum computer might be able to retroactively decrypt today’s internet communications. So Google is addressing the problem today by testing a post-quantum key exchange algorithm in Chrome, which should ideally protect from such future attempts.
Confused? Yes, quantum computing is a tough concept to get your head around (check the video below for a solid explanation). The simplified version is that quantum computers use the principles of quantum physics, which governs the behavior of subatomic particles, to perform tasks faster than a transistor-based computer.
So what is this post-quantum cryptography Google is talking about? In this context, “post-quantum” simply means secure against attacks by a quantum computer.
Specifically, Google is using a promising post-quantum algorithm called New Hope (a technical explanation is here, in case you’re one of the nine people in the world who can understand it). Google is using it on top of the existing crypto algorithm, in case New Hope turns out to be breakable with today’s computers.
You read that right: The post-quantum algorithm protects you from hackers from the future, but it might be vulnerable against today’s machines. Conversely, the elliptic-curve algorithm Google is normally using might be worthless against future’s quantum computers, but it’s the best option against the computers of today.
“We’re announcing an experiment in Chrome where a small fraction of connections between desktop Chrome and Google’s servers will use a post-quantum key-exchange algorithm in addition to the elliptic-curve key-exchange algorithm that would typically be used,” Google Software Engineer Matt Braithwaite wrote in a blog post Thursday, pointing out that Google plans to discontinue the experiment after two years, and hopefully move on to an even better algorithm.
“While it’s still very early days for quantum computers, we’re excited to begin preparing for them, and to help ensure our users’ data will remain secure long into the future,” he wrote.
What does all this mean for Chrome users? Not much. Regular users won’t be part of the test. Those who want to have a fraction of their online communication protected with a post-quantum key exchange algorithm should install the latest Chrome Canary build. To check whether post-quantum crypto was on, go to a HTTPS-secured page, click on the lock next to the URL in the address bar, click on “details,” and check if Key Exchange starts with “CECPQ1”.

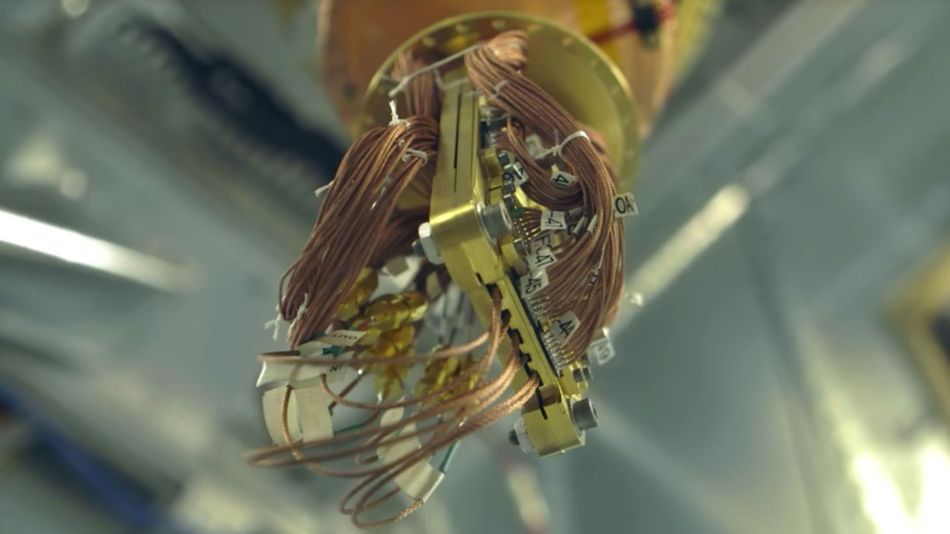
IMAGE: GOOGLE
Doesn’t sound that exciting? Well, it will be when hackers from an advanced future civilization crack every single bit of encrypted data anyone has ever sent online — except your Kung Fu Panda 3 Play Store download.
First appeared at Mashable





